End-to-end encryption (E2EE) is a method of secure communication that keeps your data private from everyone except you and the person you’re communicating with. Think of it as sending a message inside a locked box where only the intended recipient holds the key. No one in between—not even the company that runs the app—can peek inside.
What Is End-to-End Encryption, Really?

Let’s use a simple analogy to understand why this matters. Imagine you want to send a secret message through the mail.
If you use no encryption, it’s like writing your message on a postcard. Anyone who handles it—the mail carrier, the sorting facility staff—can read it. Your information is completely out in the open.
A much more common approach is encryption in transit. This is like putting your letter in a standard envelope. It’s protected from prying eyes while it travels from one post office to the next, but the postal service itself can open and read the contents if they want or need to. Many online services work this way; your data is safe from outside hackers, but the company providing the service can access it on their servers.
The E2EE Difference
This is where end-to-end encryption changes everything. In our mail analogy, E2EE is like putting your letter inside a high-tech lockbox before it even leaves your house. The only person on Earth who has the key to open that box is your recipient.
The postal service (the platform or app you’re using) can still transport the box, but they have absolutely no way to see what’s inside.
The core principle of E2EE is that data is encrypted on the sender’s device and can only be decrypted by the recipient’s device. This ensures true privacy because the service provider is mathematically locked out.
This distinction is what modern digital privacy is all about. Without E2EE, you are placing your trust in a third party to safeguard your private conversations and data. With E2EE, trust isn’t required. For another great simplified explanation of end-to-end encryption, check out this resource.
The table below clearly breaks down the differences in these security methods, showing exactly who can access your information in each scenario. It’s a powerful visual that shows just how much protection E2EE offers.
Comparing Data Security Methods
| Security Method | Data Protection Level | Who Can Access Data |
|---|---|---|
| No Encryption | None: Data is sent in plain text. | Sender, Receiver, Service Provider, Hackers |
| Encryption in Transit | Partial: Data is encrypted between your device and the server. | Sender, Receiver, Service Provider |
| End-to-End Encryption | Maximum: Data is encrypted on the sender’s device and decrypted only on the recipient’s. | Sender, Receiver |
As you can see, only E2EE truly limits access to just the sender and receiver. If you’re a developer looking to provide this level of security to your users, you can learn how to implement end-to-end encryption and make your application a trusted, private space.
How End to End Encryption Actually Works
So, how does this digital privacy shield actually work its magic? The process behind end-to-end encryption is a brilliant bit of security engineering that relies on a concept called asymmetric cryptography, which you might also hear called public-key cryptography.
Let’s break it down with an analogy. Imagine everyone using a secure app gets two special keys: a public key and a private key.
- Public Key: Think of this as a personalized, open mailbox. You can hand out copies of this mailbox to anyone in the world. They can drop a letter inside, but they can’t open it once it’s in there.
- Private Key: This is the only key that can unlock your mailbox. You guard it with your life, keeping it stored securely on your device. It never, ever leaves.
These two keys are mathematically tied together, but you can’t figure out the private key just by looking at the public one. This one-way street is the secret sauce that makes E2EE so secure.
Tracing a Message’s Journey
When you send a message to a friend, this entire security dance happens in the background in milliseconds. Here’s a simple, step-by-step look at how your message gets from your phone to theirs without anyone being able to peek.
- Requesting the Mailbox: When you start a chat, your app asks for your friend’s public key (their open mailbox). Their device sends it over.
- Locking the Message: Before your message even leaves your device, your app uses your friend’s public key to encrypt it. This scrambles your text into an unreadable jumble called ciphertext.
- Secure Transmission: The locked message now travels across the internet, passing through the service’s servers on its way to your friend. If a hacker or even the company itself intercepts it, all they’ll see is gibberish.
- Unlocking the Message: Once the message arrives, your friend’s app uses their unique private key—which has been sitting safely on their phone the whole time—to unlock and decrypt the message back into plain, readable text.
This visualization clearly shows the journey, from encryption on the sender’s device to decryption on the recipient’s.
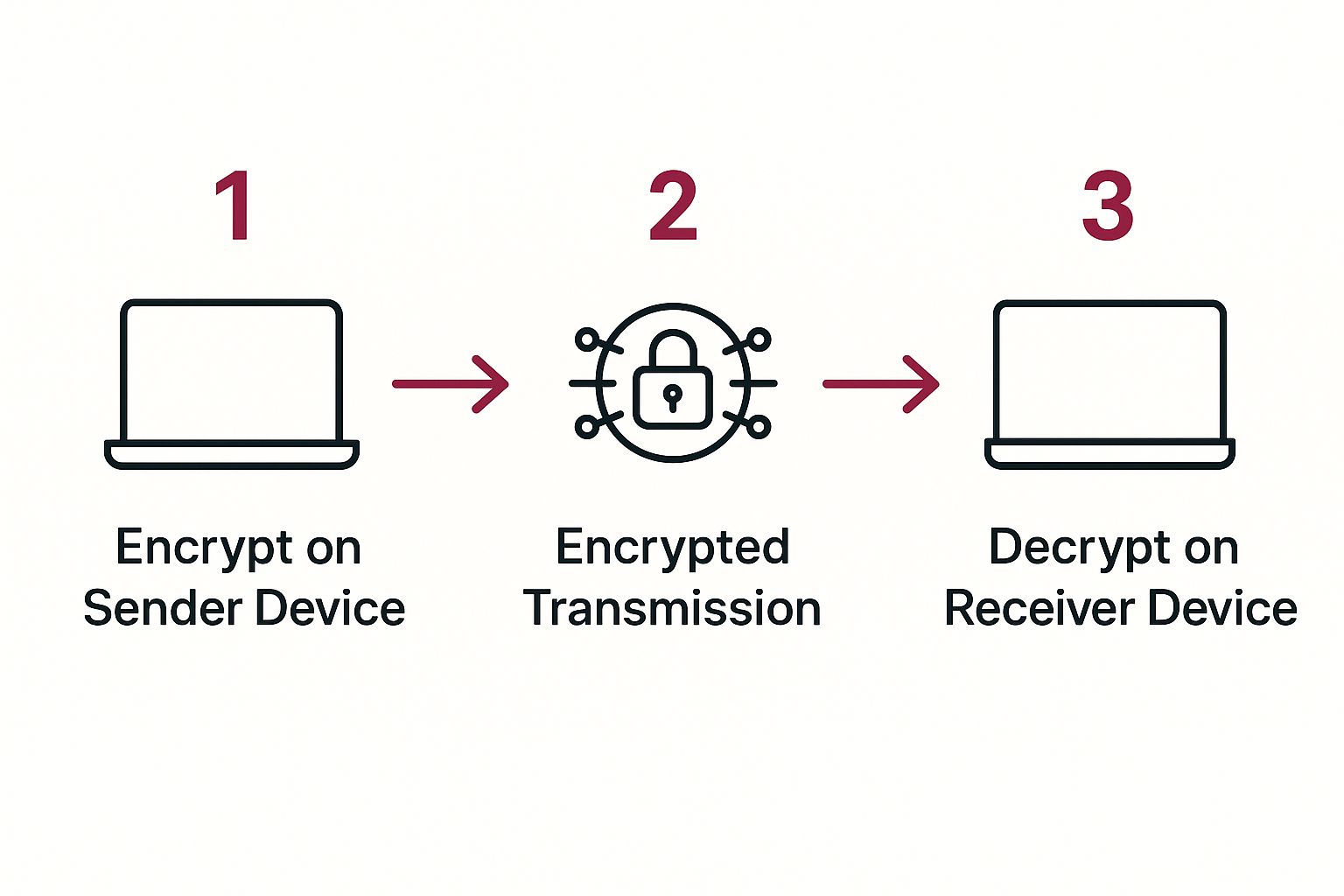
The key takeaway? The server in the middle is just a courier. It passes along the locked box but never has the key to open it.
Security That Just Works
The most impressive part of modern E2EE is how this complex exchange is completely invisible to the user. You just type and hit send. The app takes care of all the heavy lifting—managing keys, encrypting, and decrypting—without you ever noticing.
The fundamental promise of E2EE is that your message content is never exposed to anyone in the middle. It only exists in its readable form on the “ends”—the authorized devices of the sender and receiver.
This is what guarantees that not even the company that runs the service can read your private chats. It’s a world away from “encryption-in-transit,” where a service provider holds the keys and can decrypt your data on their servers. This continuous protection creates a genuinely private channel for your communications.
Where You Already Use End-to-End Encryption

You might think of end-to-end encryption as something reserved for spies or cybersecurity fanatics. The truth is, it’s already a massive part of your daily digital life. It works silently in the background, protecting your most sensitive information, and you probably use it dozens of times a day without a second thought.
The most obvious example is in secure messaging apps. Platforms like Signal and WhatsApp built their entire reputations on providing E2EE by default. Every time you send a text, share a photo, or start a video call, that data is locked on your device and can only be unlocked by the person you’re communicating with. It’s a digital cone of silence for your conversations.
It’s Not Just for Private Messaging
But E2EE’s reach extends far beyond chatting with friends. Its power to create a genuinely secure channel makes it a cornerstone for any industry where confidentiality isn’t just a feature—it’s a requirement.
Think about your financial life. When you log into your banking app or buy something online, powerful encryption protocols are working hard. Many of the services you rely on, especially financial ones, use this technology to keep your details safe. You can learn more about how secure payment methods work to protect your information.
This same demand for security is driving its adoption in other critical sectors:
- Healthcare: Telehealth consultations and electronic health records (EHRs) depend on E2EE to safeguard patient information. This is fundamental for maintaining HIPAA compliance and, more importantly, patient trust.
- Cloud Storage: Many secure cloud providers now offer “zero-knowledge” encryption. This means your files are encrypted on your computer before they even get uploaded. The provider simply stores the encrypted blob, ensuring even they can’t peek at your personal documents, photos, or business data.
- Professional Communications: From the videoconferencing tools that host sensitive business meetings to the VPNs that shield your internet traffic from prying eyes, E2EE is often the technology making it all possible.
The core value here is simple: E2EE eliminates the need for blind trust. Instead of just hoping a company will protect your data, it provides a mathematical guarantee that they can’t access it in the first place.
The New Standard for Digital Trust
From e-commerce and finance to education and remote work, end-to-end encryption is quickly becoming the baseline for privacy. It’s what secures everything from a student’s records and your credit card details to confidential business plans being discussed over a call.
Once you realize just how often you encounter end-to-end encryption, you start to see its real value. It’s the invisible shield that makes secure and private interactions a reality for everyone on the modern internet.
Why End-to-End Encryption Is So Important

In a world where data collection is constant and cyber threats are always changing, the need for end-to-end encryption has become undeniable. It’s no longer just a feature for tech-savvy users. Instead, it’s a basic requirement for anyone who values their personal privacy and for businesses that need to survive.
Think of E2EE not as an optional extra, but as a fundamental shield for your digital life. Its most obvious benefit is complete data privacy. When your messages and files are end-to-end encrypted, no one can snoop on them—not the service provider, not advertisers, and certainly not hackers.
Beyond just keeping secrets, E2EE also guarantees data integrity. This is a crucial concept. It means the message you send is precisely the one that arrives at the other end, without any meddling or manipulation along the way. This ensures the information is authentic and trustworthy from start to finish.
Protecting Your Business and Your Bottom Line
For any business, the stakes are incredibly high. A failure to protect sensitive data can lead to financial ruin and a shattered reputation. That’s why E2EE has become such a critical tool for managing risk and staying compliant.
The average cost of a single data breach is now in the millions of dollars. Suddenly, strong security isn’t just a good idea; it’s a financial necessity. This is why modern cybersecurity plans rely so heavily on E2EE to safeguard data, especially in complex setups like hybrid clouds.
E2EE is also essential for meeting tough data protection laws, such as:
- GDPR (General Data Protection Regulation): Making user data unreadable to outsiders is a core part of complying with Europe’s strict privacy rules.
- HIPAA (Health Insurance Portability and Accountability Act): For healthcare, E2EE is vital for protecting sensitive patient records and avoiding the massive fines that come with a breach.
By putting strong encryption in place, a company doesn’t just protect its users; it protects itself from legal trouble and the brand damage that always follows a security incident. When developing an application, it’s critical to follow established mobile app encryption best practices to build this foundational layer of trust.
The Limits and Myths of End-to-End Encryption
While end-to-end encryption is a powerhouse for privacy, it’s not a magic shield against every digital threat. Knowing its limitations is just as important as understanding its strengths. Having a realistic view helps you make smarter security decisions and sidestep some common traps.
One of its biggest practical drawbacks is actually a consequence of how secure it is: data recovery is often impossible. If you lose your phone or can’t remember your password, there’s no “forgot my password” button for your encrypted data. The service provider never has your keys, so they simply can’t help you get your messages back.
This “no-backdoor” design means you, and only you, are responsible for your access. It’s a serious trade-off—you gain absolute privacy but lose the convenience of recovery options.
Debunking Common E2EE Myths
Beyond these practical limits, a few pervasive myths can create a false sense of security. It’s crucial to separate what E2EE actually does from what people think it does. Getting this right is fundamental to your overall digital safety. For a deeper dive into this area, check out our complete guide on mobile security.
A widespread myth is that E2EE makes you completely anonymous. It absolutely does not.
End-to-end encryption protects the content of your communications, but it does not hide the metadata. This means details like who you’re talking to, when you sent the message, and from what location can still be visible.
This metadata can reveal a surprising amount about your activities, even if the messages themselves are unreadable. Think of it like a sealed envelope: the mail carrier can’t read the letter inside, but they still know who sent it, where it’s going, and when it was mailed.
Another common misconception is that E2EE protects your devices. It secures your data in transit, but it can’t do anything about vulnerabilities on the endpoints themselves. If your phone or computer is compromised with malware, an attacker could simply read messages before they get encrypted or right after they’re decrypted.
The takeaway? See E2EE as one critical layer in a bigger security strategy, not the entire solution. When you combine it with strong device security and an awareness of its limits, you create a much more robust defense.
The Future of Digital Privacy with E2EE
As more of our lives move online, end-to-end encryption is shifting from a nice-to-have security feature to a fundamental expectation. Let’s be honest, people are tired of their data being exposed. This isn’t just a trend; it’s a foundational change driven by both user demand and increasing regulatory pressure. The future of E2EE isn’t just about becoming more common—it’s about becoming absolutely essential.
You can see this shift reflected in market growth. The global end-to-end email encryption market, for example, is expected to balloon into a multi-billion dollar industry over the next decade. This isn’t just a number; it represents a massive wave of adoption, especially among businesses in North America and Europe that are scrambling to get ahead of cyberthreats and comply with strict privacy laws like GDPR and HIPAA. For a deeper dive into these numbers, you can find key market insights on Market.us.
The Next Frontier for Encryption
Today’s encryption is strong, but the digital world never stands still. New challenges are already on the horizon, pushing the technology to evolve.
Two major developments are shaping the future of what E2EE can do:
- Post-Quantum Cryptography (PQC): We’re hearing more and more about the theoretical threat of quantum computers—machines powerful enough to crack today’s encryption standards. To get ahead of this, researchers are already developing “quantum-resistant” algorithms. This proactive work ensures our data remains secure long into the future, even when the computing landscape changes dramatically.
- Zero-Knowledge Security: This is a fascinating concept gaining traction, especially in cloud services. Imagine a service being able to verify a piece of information without ever seeing the information itself. That’s the core idea. It allows apps to perform useful functions without ever compromising the raw user data, striking a perfect balance between utility and privacy.
E2EE’s Role in a Smarter World
The explosion of AI and smart devices presents a modern paradox: these tools need access to our personal data to be helpful, but that same access creates huge privacy risks. This is where E2EE steps in. It provides the framework to reconcile this conflict, allowing for secure data processing without exposing the underlying information to service providers. It’s how we ensure that as our technology gets smarter, our privacy doesn’t get left behind.
The future of digital privacy hinges on our ability to build systems where security is a default, not an afterthought. E2EE is the cornerstone of this vision, providing the technical foundation for a more private and trustworthy digital existence.
For developers, keeping up with these changes is non-negotiable. Just as E2EE protects user data on its journey, protecting the integrity of your application’s code is just as vital. This is where a holistic security mindset comes in. Secure code deployment, like enabling automatic app updates, is a critical piece of the puzzle. By embracing E2EE and other secure development practices, we aren’t just building better apps—we’re building a safer internet for everyone.
Common Questions About End-to-End Encryption
So, we’ve covered the what and the how of end-to-end encryption. But as with any powerful technology, diving into the details often brings up some really important questions. It’s a fantastic tool, but it’s not a magic shield. Let’s tackle some of the most common queries to get a clearer, more practical picture of where E2EE fits into our digital lives.
Is End-to-End Encryption Completely Unbreakable?
This is the big one. While the core encryption algorithms—the mathematical formulas doing the heavy lifting—are for all practical purposes unbreakable by today’s computers, that doesn’t mean the entire system is 100% foolproof.
The real weak points aren’t in the encryption itself, but at the endpoints. Think about it: if an attacker manages to infect your phone or computer with malware, they could simply read your messages after you decrypt them or capture your keystrokes before they even get encrypted. This is why E2EE has to be part of a bigger security strategy, reinforcing the need for strong device hygiene and solid application security best practices.
Does E2EE Hide Who I’m Communicating With?
Not exactly. This is a critical distinction to understand. E2EE is designed to protect the content of your messages—the words, photos, and files you send. It does not hide the metadata.
What’s metadata? It’s the “who, when, and where” of your communication.
- Who you sent a message to
- What time you sent it
- How frequently you talk to that person
Your service provider, and potentially others, can often see this information. So while the what you’re saying is kept secret, the fact that you’re communicating at all is not.
If E2EE Is So Secure, Why Doesn’t Every Service Use It?
You’d think it would be everywhere by now, right? There are a few practical hurdles that explain why it isn’t universal—at least not yet.
First, implementing E2EE correctly is genuinely difficult. It gets especially tricky for services that want to offer features like seamless multi-device syncing or cloud backups. Each of these features can accidentally create a loophole if the implementation isn’t absolutely perfect.
Second, some business models just don’t align with it. Many free services make their money by analyzing user data to serve targeted ads or to moderate content. End-to-end encryption makes that data completely inaccessible to them, breaking their model.
Finally, for a long time, many companies simply didn’t think their users cared enough about this level of privacy to make it a priority. That mindset is changing fast as people become much more aware of and concerned about their digital privacy.
At CodePushGo, we believe security and speed should go hand-in-hand. That’s why we secure our over-the-air updates with end-to-end encryption, ensuring your code remains private from our servers to your users’ devices. Learn more about deploying secure, instant updates for your React Native app at https://codepushgo.com.